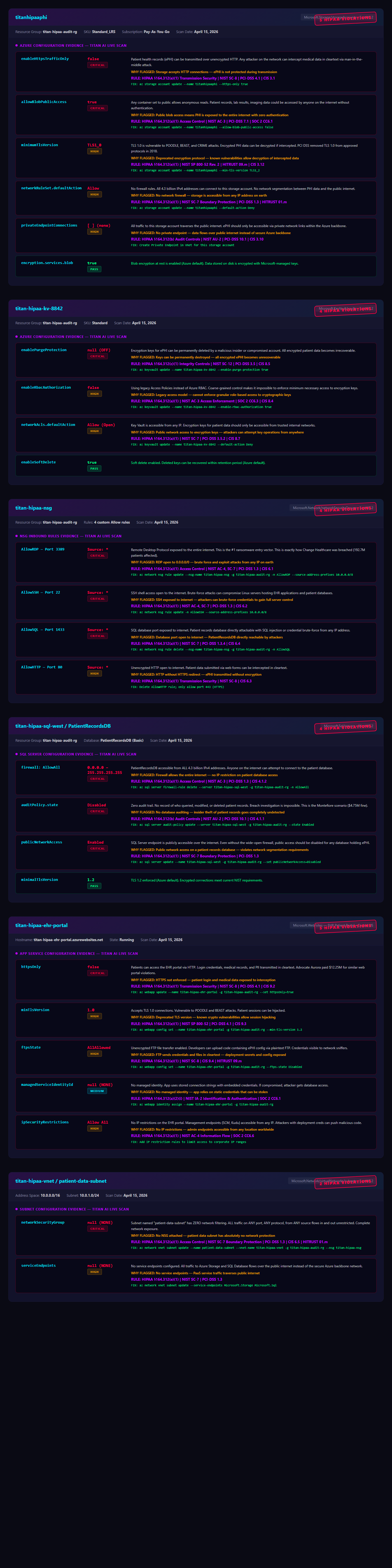
FIX ID
TITAN-FRG-FIX-0001
✔ FIXED + VERIFIED ON PROD
Azure
TITAN FORGE
CRITICAL
Public Blob Access
Disabled public blob access
■ SECTION 1 · RESOURCE IDENTIFICATION
| SUBSCRIPTION | 4f29d094-1079-44c9-acb0-4d73a7a2dd34 |
| RESOURCE GROUP | titan-lab-20260412 |
| RESOURCE NAME | titanlabdata4336 |
| REGION | East US |
| CATEGORY | Public Blob Access |
■ SECTION 2 · ACTION TAKEN
Disabled public blob access
■ SECTION 3 · REGULATORY CONTEXT
HIPAA 164.312(a)(1) + PCI DSS 1.2.1 + CIS Azure 3.1
■ SECTION 4 · BEFORE STATE
{
"allowBlobPublicAccess": true
}
■ SECTION 5 · AFTER STATE (VERIFIED)
{
"allowBlobPublicAccess": false
}
■ SECTION 6 · AI-GENERATED REMEDIATION (Claude Sonnet 4)
FIX COMMAND EXECUTED
az storage account update -n titanlabdata4336 -g titan-lab-20260412 --allow-blob-public-access false
ROLLBACK
az storage account update -n titanlabdata4336 -g titan-lab-20260412 --allow-blob-public-access true
FIX DURATION
920 ms · exit 0
■ SECTION 7 · AUDIT TRAIL
Fix ID: TITAN-FRG-FIX-0001
Applied by: TITAN FORGE
Approved by: operator consent
Applied at: April 12, 2026
Verified: ✔ re-scan confirms compliant
✔ SECTION 8 · VERIFIED: Re-scan at 2026-04-12 13:46 UTC confirmed this fix resolved the finding. Resource is now compliant.
■ SECTION 9 · EXCEPTION RECORDING & APPROVER
NO EXCEPTION ON RECORD — RISK IS ACTIVE